blog
How to Setup Centralized Authentication of ClusterControl Users with LDAP

ClusterControl 1.2.6 introduces integration with Active Directory and LDAP authentication. This allows users to log into ClusterControl by using their corporate credentials instead of a separate password. LDAP groups can be mapped onto ClusterControl user groups to apply roles to the entire group, so it is very convenient for larger organizations who have a centralized LDAP-compliant authentication system. This blog shows you how to configure LDAP authentication in ClusterControl, and allow users to use their Active Directory or LDAP username and password to log in to ClusterControl.

LDAP authentication can be configured from ClusterControl, in the Admin dashboard (ClusterControl > Admin > LDAP Settings). If you are running ClusterControl v1.2.5 or older, please upgrade to v1.2.6. It requires PHP LDAP package to be installed and enabled. To install, you can just simply use following command:
For Redhat-based:
$ yum install php-ldap
For Debian-based:
$ apt-get install php5-ldap
You may need to restart Apache web server to ensure that PHP LDAP is loaded properly. If you are upgrading your ClusterControl installation using the s9s_upgrade_cmon script, PHP LDAP will be installed automatically.
Organization Structure
The following is a simple organization structure running on OpenLDAP:
dc=severalnines,dc=org (2)
- ou=group (4)
- cn=Database Administrator
- cn=Manager
- cn=System Administrator
- cn=Programmer
- ou=people (4)
- cn=Eric Steven
- cn=Matthew Carey
- cn=Michael Joshua
- cn=Ronnie Harp
We want to assign each of them to the appropriate role in ClusterControl:
|
LDAP User |
LDAP Group |
ClusterControl Role |
Description |
| Eric Steven | System Administrator | Admin | View, modify, delete clusters |
| Matthew Carey | Programmer | User | Access only clusters he has added |
| Michael Joshua | Database Administrator | Super Admin | View, modify, delete all clusters |
| Ronnie Harp | Manager | Manager | View all clusters |
Managing Roles in ClusterControl
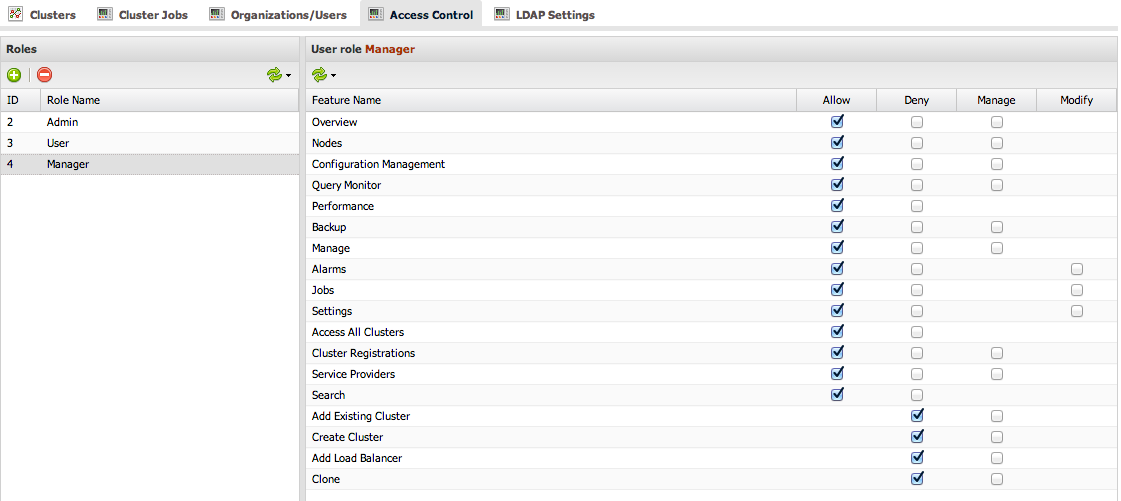
ClusterControl default roles are Super Admin, Admin and User. We need to create a new role for our “Manager” group so users in that group can view all clusters but not modify them. So, we will create a new role, ‘Manager’, under ClusterControl > Admin > Access Control and assign it with the appropriate privileges:
Looks good. Now we can proceed to integrate our LDAP authentication with ClusterControl.
Integrating with LDAP
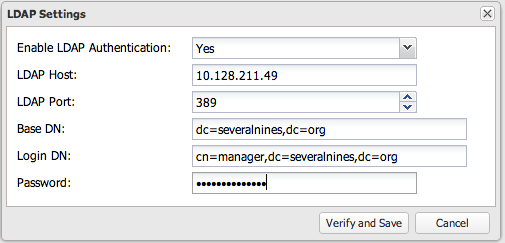
Go to ClusterControl > Admin > LDAP Settings and specify the required LDAP server details, as per screenshot below:
The following describes the required LDAP settings:
|
Field |
Description |
| Enable LDAP Authentication | Choose whether to enable or disable LDAP authentication. |
| LDAP Host | The LDAP server hostname or IP address. To use LDAP over SSL/TLS, specify LDAP URI, ldaps://[hostname/IP address] |
| LDAP Port | Default is 389 and 636 for LDAP over SSL. Make sure to allow connections from ClusterControl host for both TCP and UDP protocol. |
| Base DN | The root LDAP node under which all other nodes exist in the directory structure. |
| Login DN | The distinguished name used to bind to the LDAP server. This is often the administrator or manager user. It can also be a dedicated login with minimal access that should be able to return the DN of the authenticating users. ClusterControl must do an LDAP search using this DN before any user can log in. |
| Password | The password for the binding user. |
Click ‘Verify and Save’. If verification fails, ClusterControl will refuse to save the specified LDAP settings.
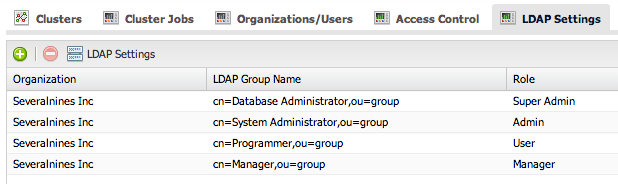
Mapping LDAP Group with ClusterControl Roles
Finally, let’s map the related LDAP group to its corresponding role in ClusterControl. This would ensure that ClusterControl authorizes the logged-in user based on the role assigned. Click ‘+’ icon and specify the LDAP group distinguished name with its respective roles. Once completed, we should have something similar to the following screenshot:
LDAP authentication setup is now complete. We can proceed to login.
Login with LDAP Credentials
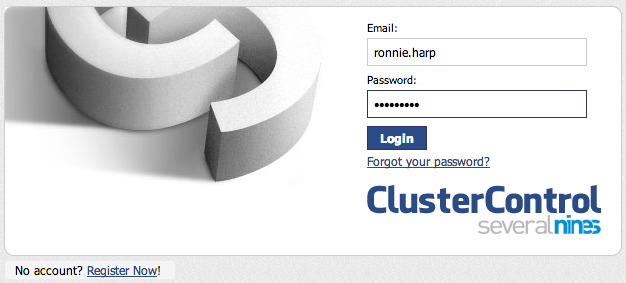
On the ClusterControl login page, specify the username and password of LDAP user credentials:
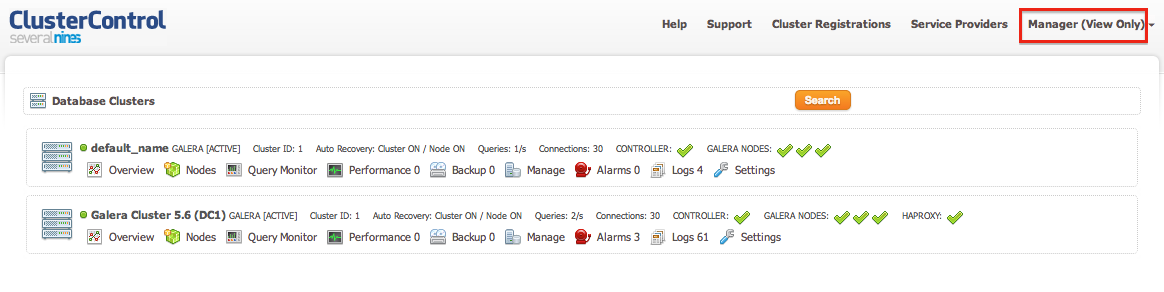
In this example, we logged in as Ronnie Harp, the IT manager who can view all clusters but not modify or delete any settings in ClusterControl. You can verify this with the user role status which appears on the top right menu, similar to the screenshot below:
That’s it. You can now login to ClusterControl using both LDAP authentication and default ClusterControl authentication.